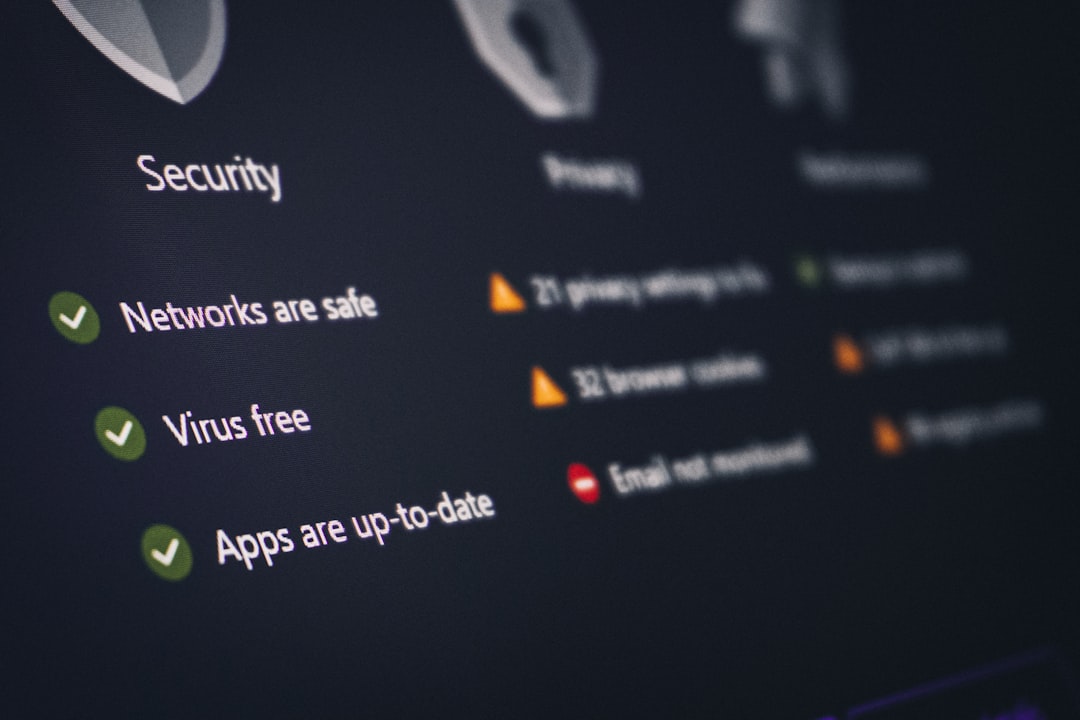
As cyber threats continue to escalate in complexity and frequency, the demand for more sophisticated defense mechanisms has never been greater. Security Operations Centers (SOCs) are at the forefront of this battle, tasked with configuring endpoint detection and response (EDR) policies under pressure from intelligent adversaries. The need for formal guarantees in decision-making processes has led researchers to explore novel architectures that can ensure reliable and effective outcomes in high-stakes environments. The recent introduction of a tool-mediated architecture for LLM agents represents a significant advancement in this domain, providing a framework that not only enhances operational efficacy but also guarantees controllability and stability in adversarial scenarios.
The proposed architecture employs a combination of deterministic tools, including Stackelberg best-response strategies, Bayesian observer updates, and attack-graph primitives, which are critical for navigating the complexities of cyber defense. LLM agents leverage these tools to select from a finite action catalog, ensuring that their outputs are aligned with the operational requirements of SOCs. Central to the implementation is a composite Lyapunov function, which has been rigorously machine-checked in Lean 4, a formal proof management system. This function certifies key properties such as controllability, observability from asymmetric sensor data, and Input-to-State Stability (ISS), offering robust assurances against intelligent adversarial disturbances.
In empirical evaluations, the effectiveness of this architecture is underscored by its performance on 282 real enterprise attack graphs. The results indicate that the tool-mediated Claude Sonnet 4 controller yields a remarkable 59% reduction in the attacker's expected payoff compared to a deterministic greedy baseline across multiple runs, demonstrating stable performance with zero variance even at varying operational temperatures. Additionally, the Claude Haiku 4.5 controller, while converging towards suboptimal game values, remains catalog-bounded, highlighting the architecture's resilience regardless of the controller's capability. This stability is pivotal, as it allows for creative exploration of strategies without compromising system integrity.
The development of LLM agents capable of learning and adapting to adversarial tactics adds a new layer of sophistication to cybersecurity measures. As these agents operate within a tool-mediated framework, they combine the computational prowess of LLMs with deterministic decision-making processes, ensuring that they can effectively respond to a wide array of threats. This integration not only enhances their strategic capabilities but also aligns with the operational constraints imposed by real-world cyber environments.
Contextually, this advancement fits into the broader landscape of AI-driven cybersecurity solutions, where the intersection of machine learning and formal methods is increasingly recognized as essential for the development of trustworthy autonomous systems. The inherent unpredictability of cyber threats necessitates a paradigm shift towards systems that can autonomously adapt while maintaining formal guarantees of performance and stability. This architecture represents a step towards achieving that goal, as it encapsulates the dual requirement for creativity in strategy and robustness in execution.
CuraFeed Take: The introduction of this tool-mediated LLM architecture heralds a new era in autonomous cyber defense, where formal guarantees meet the dynamic nature of cyber threats. As organizations increasingly embrace these advanced methodologies, those that adopt such frameworks will likely gain a competitive edge in mitigating risks associated with cyber attacks. In the coming months, it will be crucial to observe how these architectures are integrated into existing cybersecurity infrastructures and the subsequent impact on incident response times and effectiveness against sophisticated adversaries. The success of these systems may very well redefine standard practices within SOCs, ultimately reshaping the future landscape of cybersecurity.